How to Correctly Work With HTTPS Certificates
The article is intended for customers who are using their own servers for hosting eWay-CRM.
If you are using hosting on eWay-CRM domain, there should be no issues with certification. If you are experiencing some certification problems on eWay-CRM domain, please contact us immediately.
Certificate Issued by Common Trusted Certification Authority (Safest Option)
eWay-CRM is using this security on its domains.
Server certificate is issued by the common trusted certification authority. Verifying certificates are standard part of operating systems (Android, iOS, Microsoft Windows, etc.). HTTPS communication with server that is signed with this certificate is always considered as safe.
The certificate error can appear only in the case when server domain is different than domain in HTTPS certificate:
- Android never accept this certificate.
- iOS asks you whether you want to ignore the issue.
Administrator of the server should alert users of bot systems (Android and iOS) that they should not accept these notices and always tell their appearance to the administrator. The issue could be caused by hacker attack.
Note: How to Secure eWay-CRM Using SSL Certificate offers you basic information about setting SSL certificate for your eWay-CRM.
Personal Certification Authority (Safe Option)
You can issue HTTPS certificate at your own certification authority.
Personal Certification Authority on iOS
User has possibility to download verifying certificate of own personal authority and import it using Safari (only via Safari).
Then, you can find imported certificate in your Profiles:
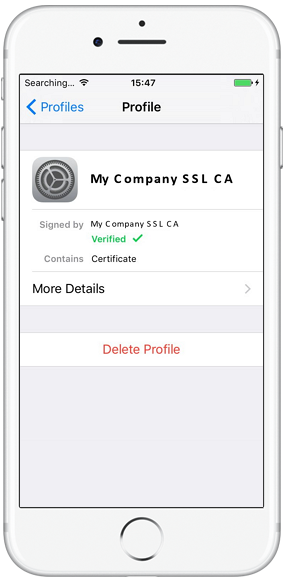
These steps are only correct. Since then, iOS will not notify about any certificate error anymore during eWay-CRM Mobile login.
If the certification dialog will appear, user does not accept it. The issue could be caused by hacker attack. Server administrator should resolve this situation.
Personal Certification Authority on Android
Android is different from iOS and it does not allow you to use the same steps as described above. Android will always show you this notification:
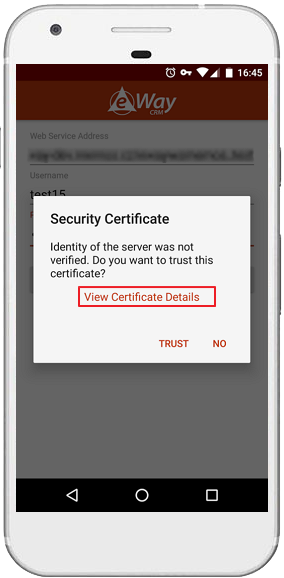
Click View Certificate Details and check whether certificate information are same as administrator generated during the creating HTTPS certificate on personal certification authority (you can compare it with certificate in Microsoft Windows).
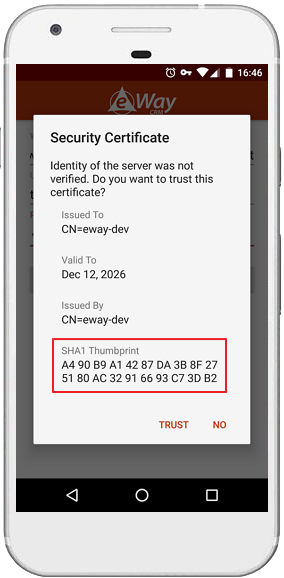
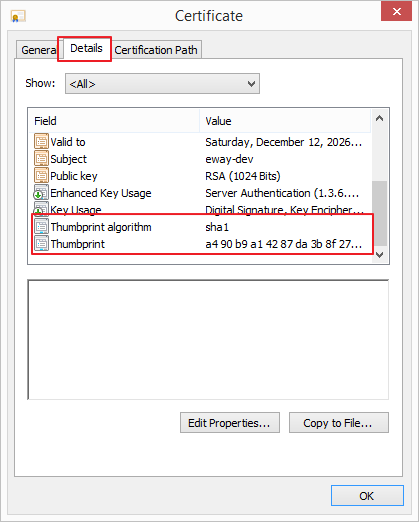
If records are same, you can trust the certificate.
Certificate will be saved to the specific storage of eWay-CRM Mobile and Android will accept it.
If the certificate will be renewed or changed, the communication will stop working - the certificate will be considered as dangerous. In this case, you need to login eWay-CRM mobile again and accept the new certificate.
Self-Signed Certificates (Less Safe Option)
Self-signed certificates have no verifying certificate from certification authority.
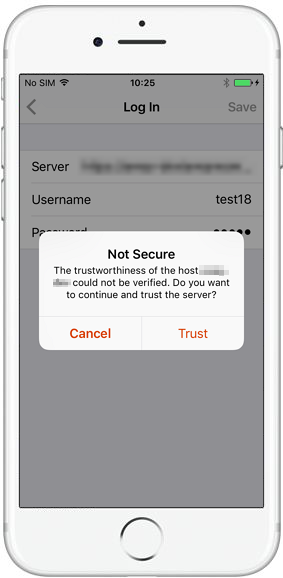
Self-Signed Certificate on iOS
System cannot import anything. iOS will always show this notification:
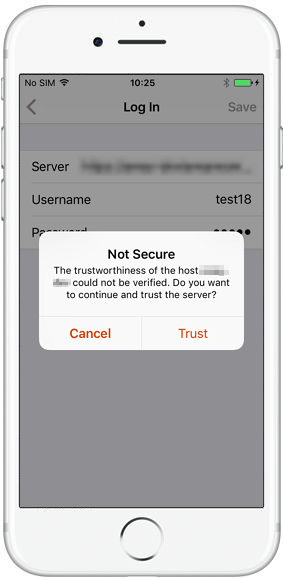
If you accept it, you set that you can trust specified domain (server) and you want to ignore issues with safety. iOS will ignore issues with safety on this domain until you uninstall eWay-CRM Mobile.
Communication on your iPhone will be encrypted, but hacker can use his or her own encrypted key.
Self-Signed Certificate on Android
Android does not consider self-signed certificate as troubled. Process is same as on the certificate issued by personal certification authority.
Summary:
- If you trust domain on iOS and accept notification, iOS will ignore safety issues related to this domain. Accept this notification only in the case you are permitted by your administrator.
- If you accept certificate notification on android, you make an exception for the specific certificate. Because of it, it is needed to check information in the certificate.
